ReQrypt - Request Encryption
ReQrypt is a free tool for bypassing a local adversary. This includes:
- ISP-level URL-filtering (a.k.a. censorship) systems;
- ISP or government data-logging/snooping systems; and
- ISP or local network forced transparent proxying.
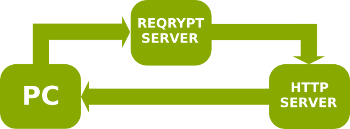
Unlike other anti-censorship tools, ReQrypt does not rely on a network of friendly proxy severs. Instead, ReQrypt works more like a user-controllable routing tool, that lets the user redirecting outbound packets through one or more encrypted tunnel(s) -- bypassing the local adversary. ReQrypt does not affect inbound traffic, which is sent via the normal route.
ReQrypt has the following advantages:
- Since ReQrypt does not rely on proxy servers, your IP address will not be changed. To the remote web server, it appears as though your traffic was sent directly from your PC unchanged (save for TTL values and fragmentation).
- Since inbound packets are sent directly from the web server to your browser, and not via a proxy server, ReQrypt is fast.
- (For tunnel operators): running a ReQrypt server is cheaper than running a proxy server, since outbound traffic (web requests) is usually much smaller than inbound traffic (web responses).
ReQrypt is effective against most lightweight filtering/logging systems that are popular in western countries, since such systems usually only intercept outbound traffic. Intercepting inbound traffic is generally more expensive and technically challenging, thus is usually ignored.
ReQrypt - Getting Started
NOTE: Please keep in mind that ReQrypt can be hit-and-miss. It will either work perfectly or not work at all (and usually because of an incompatible NAT or bad configuration).
To use ReQrypt please use the following instructions:
- Download ReQrypt for your system.
- (Recommended) Make sure IPv6 is disabled, e.g.:
- Windows: Under Control Panel → Network and Sharing Center → View your active networks → Local Area Connection → Properties → Networking, click to clear the Internet Protocol Version 6 (TCP/IPv6) box and press OK.
- Linux: Run the commands as root:
sysctl net.ipv6.conf.all.disable_ipv6 sysctl net.ipv6.conf.default.disable_ipv6 sysctl net.ipv6.conf.lo.disable_ipv6 - MacOSX: Under System Preferences → Network → Ethernet and/or AirPort → Advanced → TCP/IP, set Configure IPv6 to Off and press OK.
- (Recommended) Change your DNS, e.g. use Google Public DNS.
- Start ReQrypt.
- (Optional) Configure ReQrypt.
If you have IPv6 enabled, then you must disable it before using ReQrypt. Currently ReQrypt ignores IPv6 traffic.
Many filtering systems use a combination of DNS poisoning and packet
interception.
It is therefore recommended that your change your DNS server in
addition to using ReQrypt.
If your ISP blocks external DNS traffic, you can try enabling
DNS Hiding
in the ReQrypt OPTIONS tab.
ReQrypt can be tuned based on the type of system you are trying to circumvent. See the next section on effectiveness.
ReQrypt - Effectiveness
ReQrypt is effective against many kinds of provider-level filtering, proxying and data retention systems. This is summarized in the following table:
| Filter/Proxy | ReQrypt? | Explanation |
|---|---|---|
| DNS poisoning | ✗ | ReQrypt is overkill for DNS poisoning. Instead reconfigure your system to use a different DNS server, such as Google Public DNS. |
| DNS blocking | ✓ | This occurs when your provider blocks access to alternative DNS servers. In this case reconfigure your system to use a different DNS server then run ReQrypt with Hiding mode set to "Off" and "DNS Hiding" enabled. |
| IP address blocking | ✓ | Provider blocks certain IP addresses. Use ReQrypt with "Active-Highest" mode enabled. |
| Proxy-ing | ✓ | Provider forces all HTTP traffic through proxy servers. In some cases ReQrypt can completely bypass the proxy servers with "Active-Highest" mode enabled. |
| Hybrid proxy-ing | ✓ | Provider forces some HTTP traffic through proxy servers based on IP address. As above use ReQrypt with "Active-Highest" mode enabled. |
| Hybrid filtering | ✓ | Provider blocks access to certain URLs at the Network level using Deep Packet Inspection (DPI). For Network-level filtering only the URLs need to be hidden. Use ReQrypt with "Passive", "Active-Low" or "Active-Medium" modes enabled. |
| Mirror filtering | ✓ | This is similar to hybrid filtering except the provider copies (mirrors) rather than selectively redirects packets. As above, use ReQrypt with "Passive", "Active-Low" or "Active-Medium" modes enabled. |
| URL sniffing | ✓ | Provider is sniffing packets to extract URLs for logging or data-retention purposes. User ReQrypt with "Active-Medium" mode enabled. |
| Strong filtering | ✗ | The various strong filtering methods used in countries like China or Iran. ReQrypt is generally ineffective against such systems since they typically block or severely restrict inbound traffic. |
ReQrypt - Download
ReQrypt version 1.4.1 is available for download:
-
 reqrypt_1.4.1_amd64.deb:
Debian package for 64-bit Linux.
reqrypt_1.4.1_amd64.deb:
Debian package for 64-bit Linux. -
 reqrypt-1.4.1-win64-install.exe:
Installer for 64-bit Windows 7, 8, and 10.
reqrypt-1.4.1-win64-install.exe:
Installer for 64-bit Windows 7, 8, and 10. -
 reqrypt-1.4.1-win64-files.zip:
Standalone files (i.e. no installer) for 64-bit Windows
7, 8, and 10.
reqrypt-1.4.1-win64-files.zip:
Standalone files (i.e. no installer) for 64-bit Windows
7, 8, and 10.
ReQrypt is an open source project released under GNU GPL VERSION 3.
ReQrypt - Sponsors
The ReQrypt server has been generously provided by Windscribe. We thank Windscribe for their support.
ReQrypt - Spin-off projects
- WinDivert - Divert sockets for Windows.
